Documentation
Validator: PAM
The pam validator uses the Pluggable Authentication Module to validate the username/password combination.
Parameters
Users: You can restrict to some local system users
Compatibility
This validator is compatible with the basic scheme.
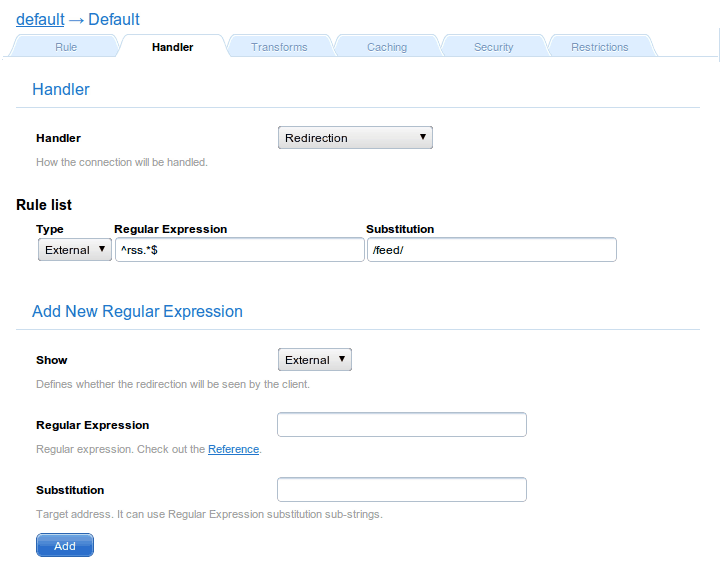
Example
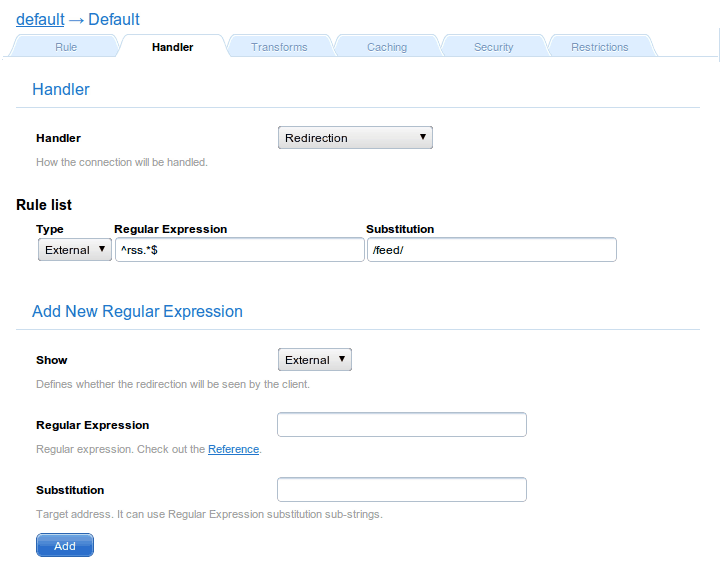
Requires a valid user and password system pair to access the protected directory. It will be available for all local users, unless a restriction list is provided.
Notes
The PAM approach ensures a dynamic configuration for how the authentication is performed. This dynamic configuration must be specified. This means that a /etc/pam.d/cherokee file must define the connection between Cherokee and the pluggable authentication modules that perform the actual authentication tasks.
Cherokee’s installation procedure already takes care of the creation of such file (under /etc or whatever system configuration directory is used in your platform of choice). If you consistently fail to use the PAM validator, make sure that such configuration definitions are set.
# # The PAM configuration file for Cherokee # account required pam_unix.so auth required pam_unix.so nullok auth required pam_env.so session required pam_unix.so
Bare in mind that Cherokee needs to be able to read /etc/shadow in order to perform PAM authentication. If you are not successful setting up this validator, check your logs for clarification about the authentication failures you might be experiencing. The solution to this particular problem is adding the user under which Cherokee is running to the shadow-group and restarting cherokee. This is easily achievable. For instance, assuming Cherokee is running as www-data on a Debian based Linux distribution, this can be done with the following command.
sudo adduser www-data shadow
